As the U.S. faces China’s unprecedented military buildup, conflicts involving our partners in two theaters, and resurgent terror threats, it is clear that the world today is more dangerous than most Americans have experienced in their lifetimes. Yet, as the U.S. Department of Defense pursues modernization programs to retain our competitive edge, we cannot afford
At CloudDefense.AI, we strive to make cybersecurity accessible and actionable. These blogs are part of our commitment to help organizations proactively defend against evolving threats.” — Anshu Bansal, CEO of CloudDefense.AI PALO ALTO, CALIFORNIA, USA, May 31, 2024 /EINPresswire.com/ — CloudDefense.AI, a leader in Cloud Security and DevSecOps solutions, is proud to announce the release
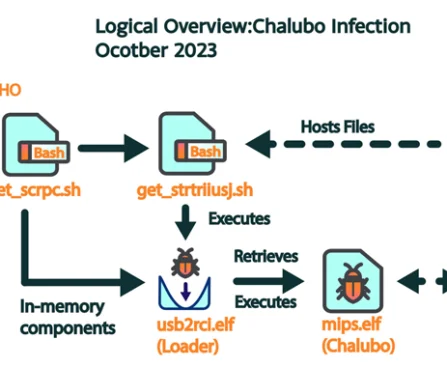
May 31, 2024NewsroomNetwork Security / Cyber Attack More than 600,000 small office/home office (SOHO) routers are estimated to have been bricked and taken offline following a destructive cyber attack staged by unidentified cyber actors, disrupting users’ access to the internet. The mysterious event, which took place between October 25 and 27, 2023, and impacted a
At the RSA Conference in San Francisco this month, a dizzying array of dripping hot and new solutions were on display from the cybersecurity industry. Booth after booth claimed to be the tool that will save your organization from bad actors stealing your goodies or blackmailing you for millions of dollars. After much consideration, I
A threat actor has breached customers of cloud storage and analytics giant Snowflake by using stolen credentials to access databases, according to cloud security vendor Mitiga. According to a blog post published Thursday, the threat actor, tracked as UNC5537, “has been observed using stolen customer credentials to target organizations utilizing Snowflake databases” to conduct data
The editors at Solutions Review have curated this list of the most noteworthy endpoint security and network monitoring news for the week of May 31. This curated list features endpoint security and network monitoring vendors such as McCrary Institute, Worcester Polytechnic Institute, NightVision, and more. Keeping tabs on all the most relevant endpoint security and
Startup founders dream of success, but it’s much harder than it looks. As a former founder, I know the challenges of cultivating an idea, establishing product market fit, growing revenue, and finding the right exit. Trust me, it doesn’t always end well. In this interview, we welcome Seth Spergel, Managing Partner at Merlin Ventures, to
NREL Explores Setup and Security of 5G for Microgrids With a 5G Sandbox NREL developed a 5G testbed to study the ability of 5G networks to facilitate microgrid controls, assess how 5G can improve microgrid operational efficiency and latency, and test its resilience against cyber threat scenarios. Photo from Getty Images Whether it is coincidence
Global Embedded Security Market to Reach Valuation of US$ 10.5 Bn by 2034; at a CAGR of 9.75% During 2024 – 2034 WILMINGTON, DELAWARE, UNITED STATES, May 31, 2024 /EINPresswire.com/ — Embedded security refers to the protection of embedded systems, which are specialized computing devices integrated into larger systems for specific tasks. These systems are